Advisory: CVE-2026-31431 Copy Fail – Local Privilege Escalation via AF_ALG/algif_aead
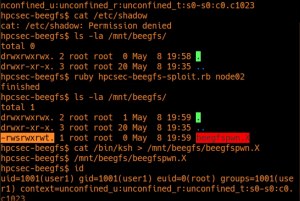
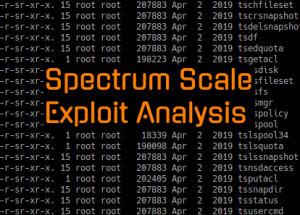
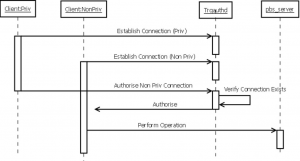
On 29th April 2026 an advisory for CVE-2026-31431 was released alongside working proof of concept code. This is a privilege escalation vulnerability which is trivially exploitable and which affects all versions of Linux released since 2017. Shortly after this was…